LOG4J – Linux & Windows Script to identify log4j Vulnerability

Dear JDisc friends,
find the German translation from our long-term partner i-doit:
https://www.i-doit.com/en/blog/jdisc-and-i-doit-it-service-management-with-discovery-and-cmdb/
I think everyone is busy figuring out if any applications are affected by the log4j security issue. While this may be easy for commercial applications, the vulnerability can be difficult to find for custom applications that are hosted in your data centers. Applications developed by external consultants that may have already switched to the next customer or project are associated with high risk. Applications are often poorly maintained or documented, making it even more difficult to identify the threat.
Therefore we wrote a script (for Linux and Windows) to check a computer for risky applications running on application servers like Tomcat, JBoss, WebSphere, or others. The script can either run on its own on a server, or it can be integrated with JDisc Discovery so that it runs every time a Linux or Windows computer is scanned.
The script is pretty simple. It tries to find the executable JAR file from the JDK first. The jar command is required to examine .jar, .ear, and .war files. When jar is not installed, then it uses unzip as a fallback. Then it looks for log4j jar files directly on the hard drive. Finally, it checks all of the .ear, .jar, and .war files by searching the archive to find any embedded occurrences of log4j. Whenever it finds an occurrence, it simply prints a notice in the console window. To minimize authorization problems, we recommend executing the command as root!
Note that not all findings might be critical. The findings are just a hint for further investigations!
We look forward to your feedback in order to improve the script or migrate to other Unix variants. We appreciate your improvements so that everyone can benefit from your changes!
The script is provided as-is without any warranty or license limitations.
How to run the Script with JDisc Discovery
In addition to running the script manually in a console window, you can let JDisc Discovery do the work for you. The idea is to take advantage of JDisc Discovery’s ability to populate custom attributes by running scripts on the target machines. Whenever JDisc Discovery scans a Linux computer, it copies the script to the destination computer, runs the script, and captures the output. The output is saved in a custom attribute that can be used later for reporting.
Unfortunately, the configuration is not the most intuitive piece of UI I have ever written :-(.
The following steps explain how to integrate the script into your discovery.
Download the Script
Download the script and save it locally on your disk. Please be aware that the file uses Unix line endings. Changing it to Windows line endings (by editing the file) might cause issues! So make sure that it still has Unix line endings after your changes!
Define a new Custom Attribute
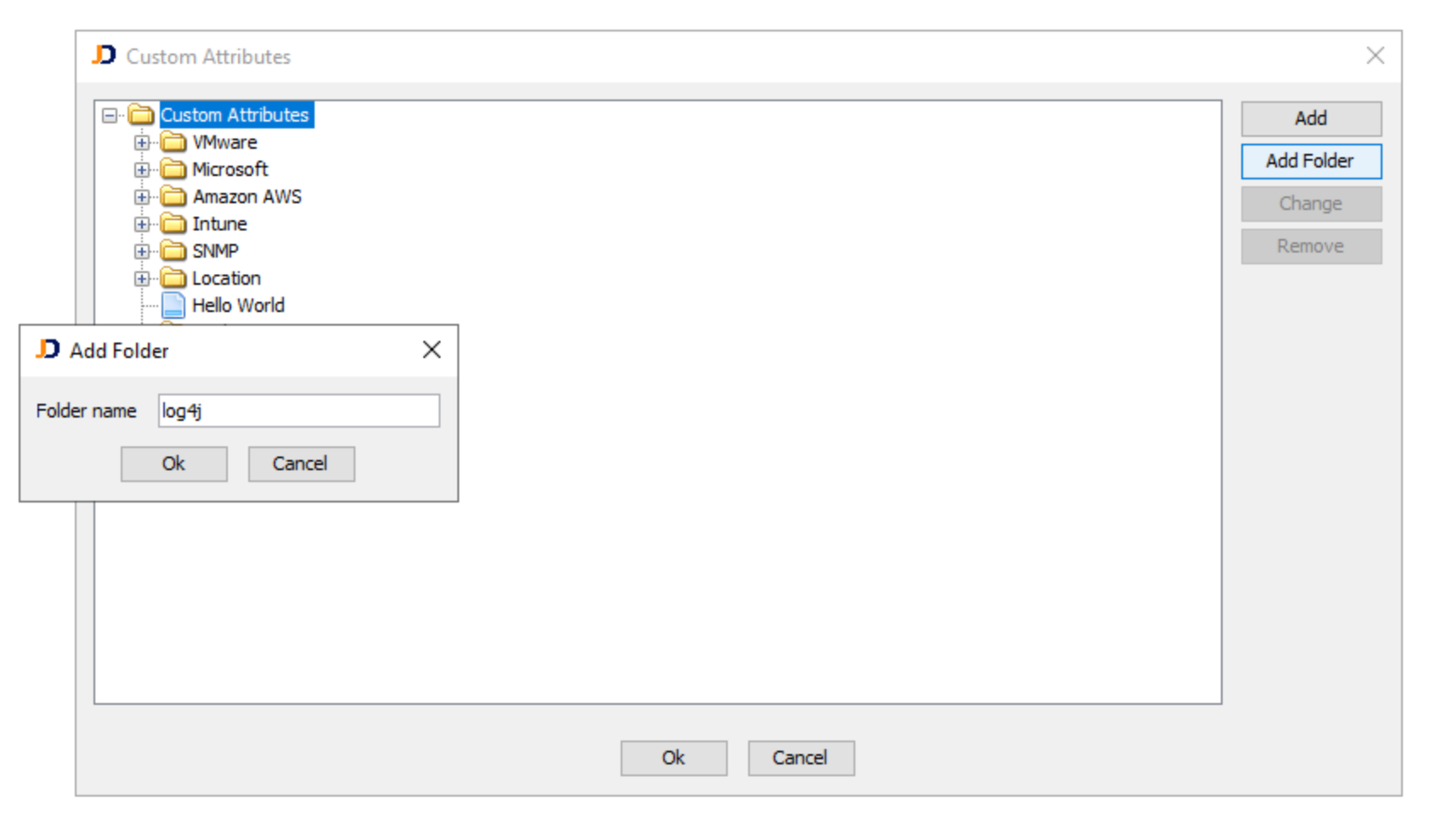
Open the menu item Devices > Custom Attributes > Configuration. That’ll bring up the dialog for the custom attribute collection. Add a new folder named “log4j” by clicking on the Add Folder button.
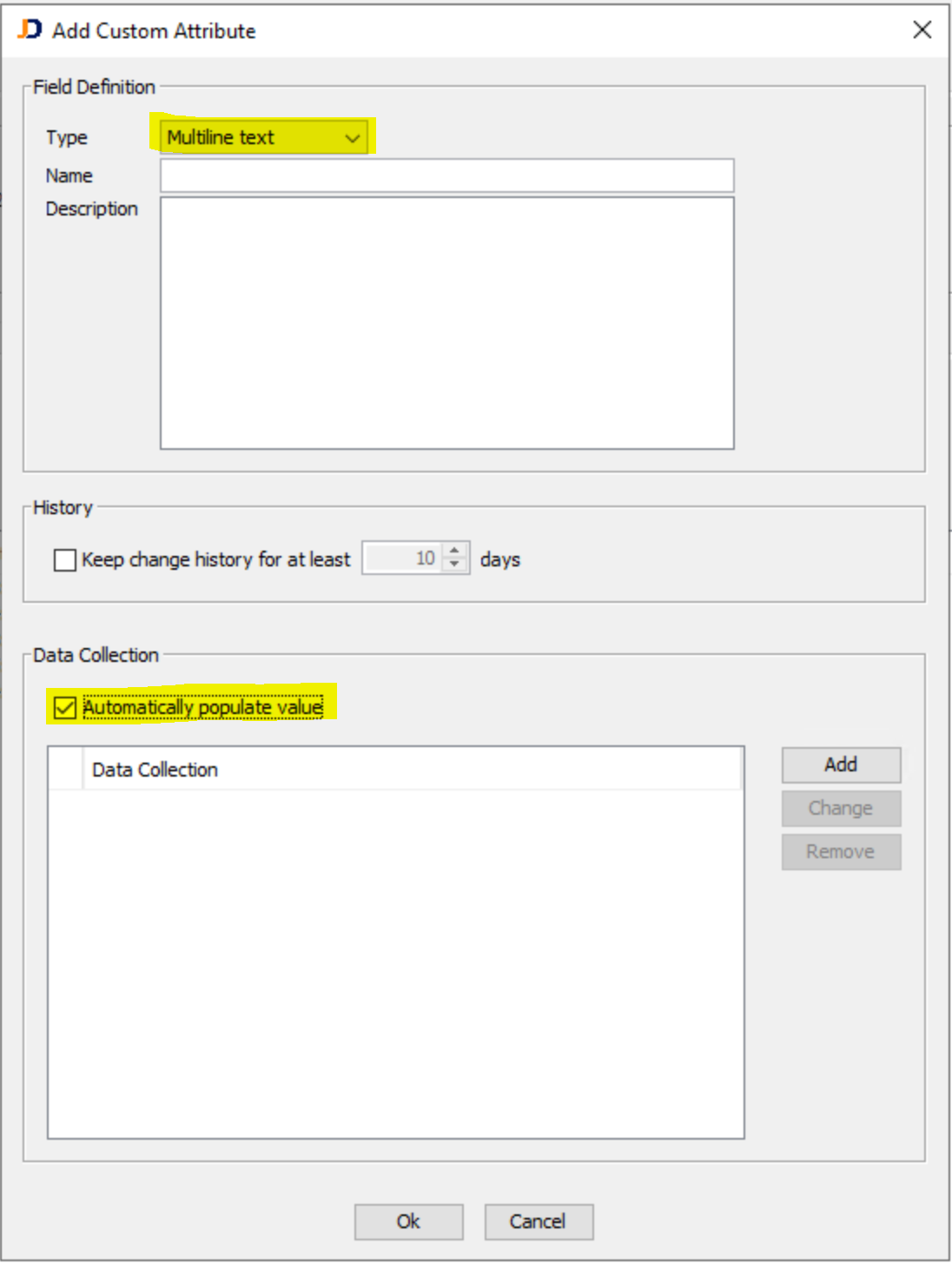
Then select the log4j folder and click on the Add button. Then select the content type Multiline Text and make sure that the checkbox Automatically populate value is selected.
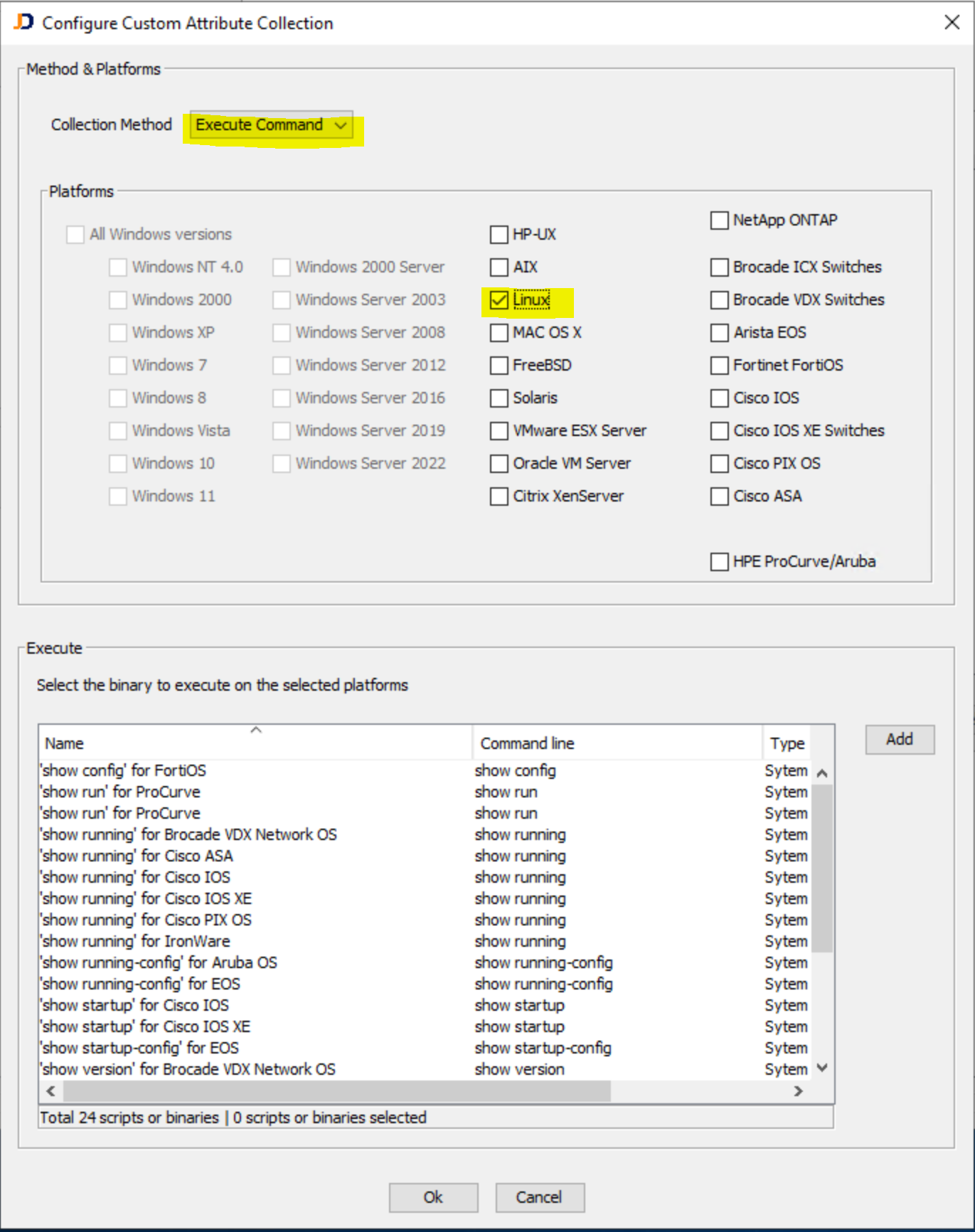
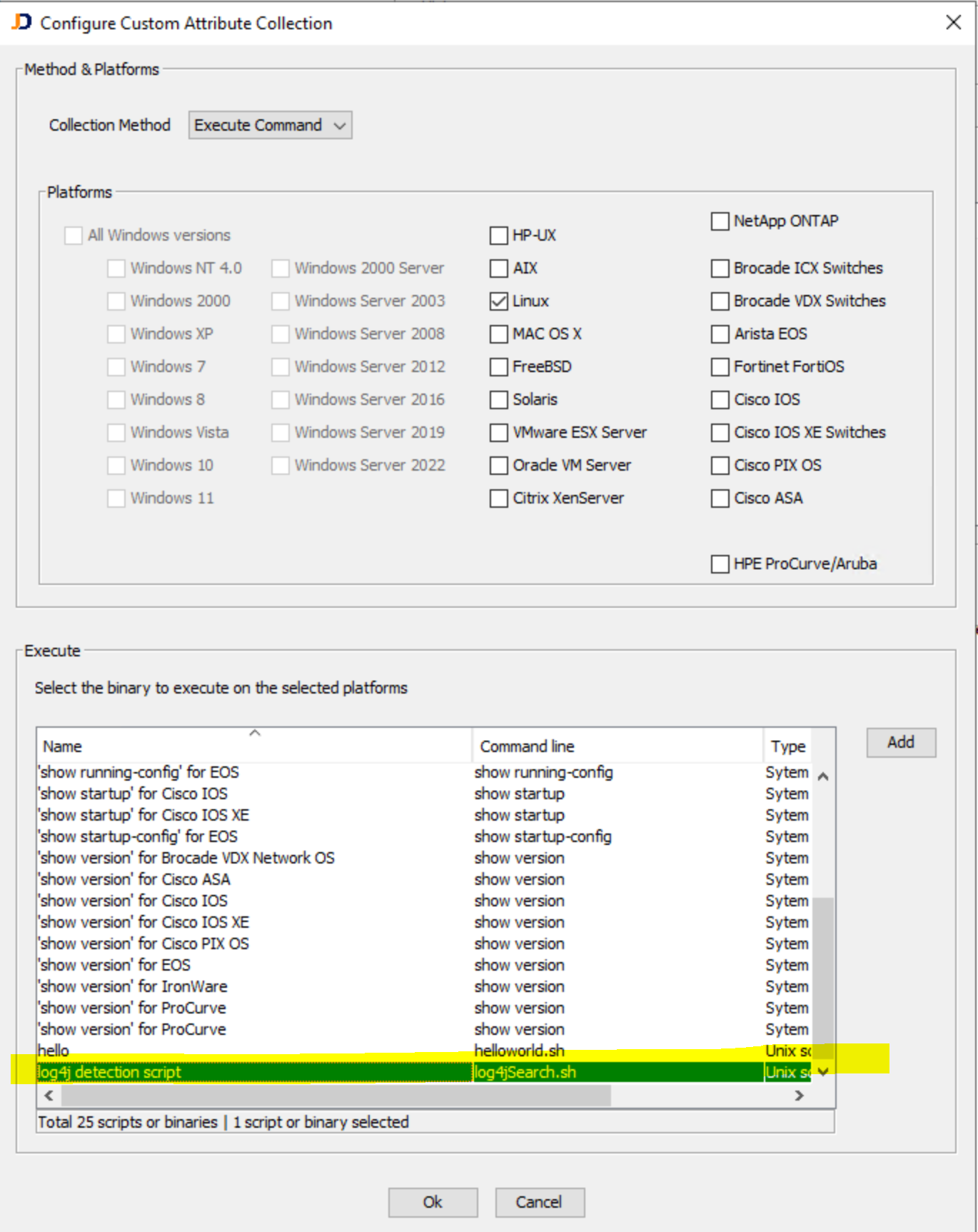
Then click on the Add button to add a new collection method. Make sure to change the Collection Method to Execute Command. Also, make sure to select the platform Linux (or All Windows versions in case you run the Windows script) to deploy the script only on Linux (or Windows).
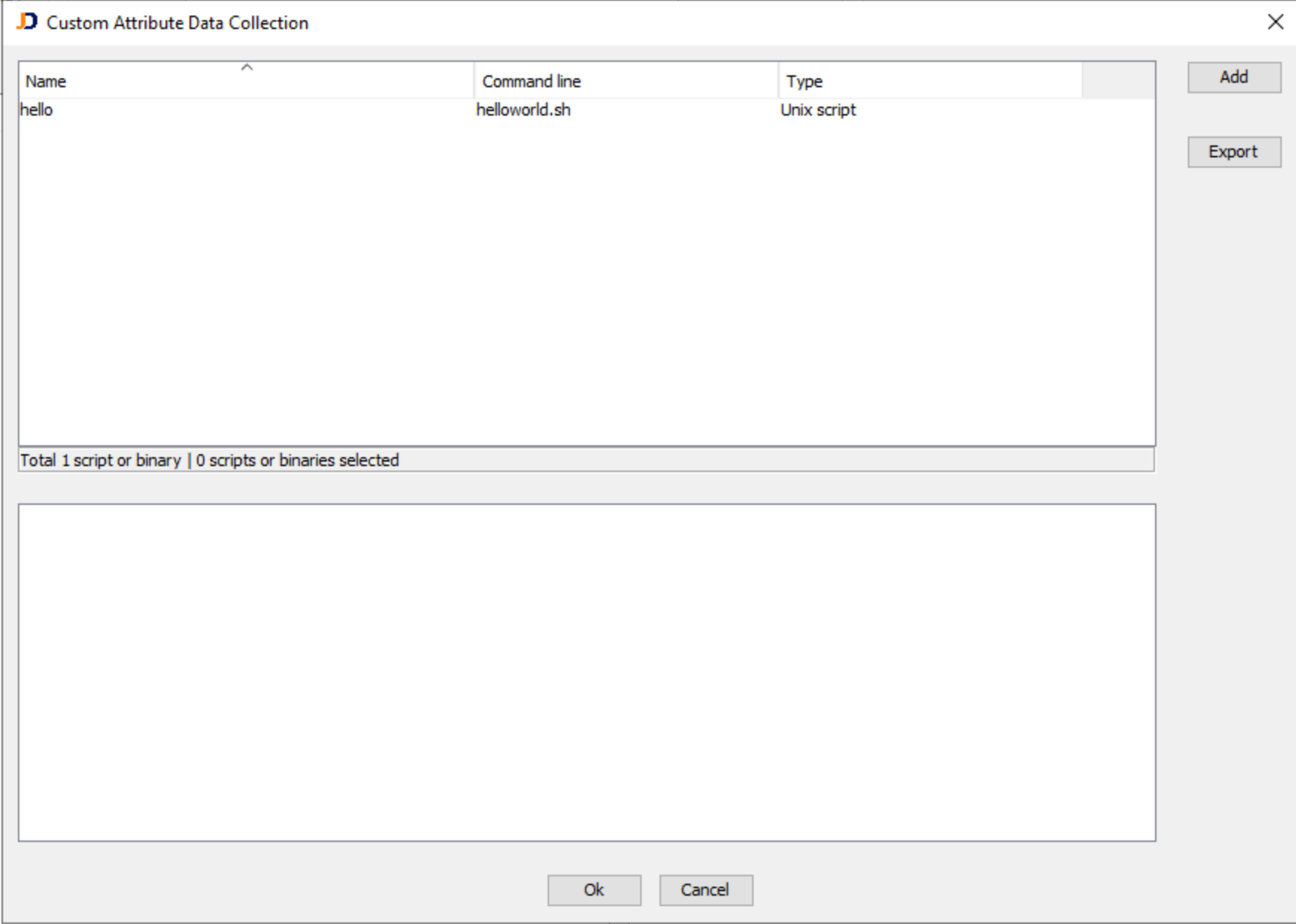
Now click again on the Add button in order to add a new collection script. That’ll bring up a new dialog box with the list of existing collection scripts. In my case, I already have a “helloworld.sh” test script. In your case, it is most probably empty.
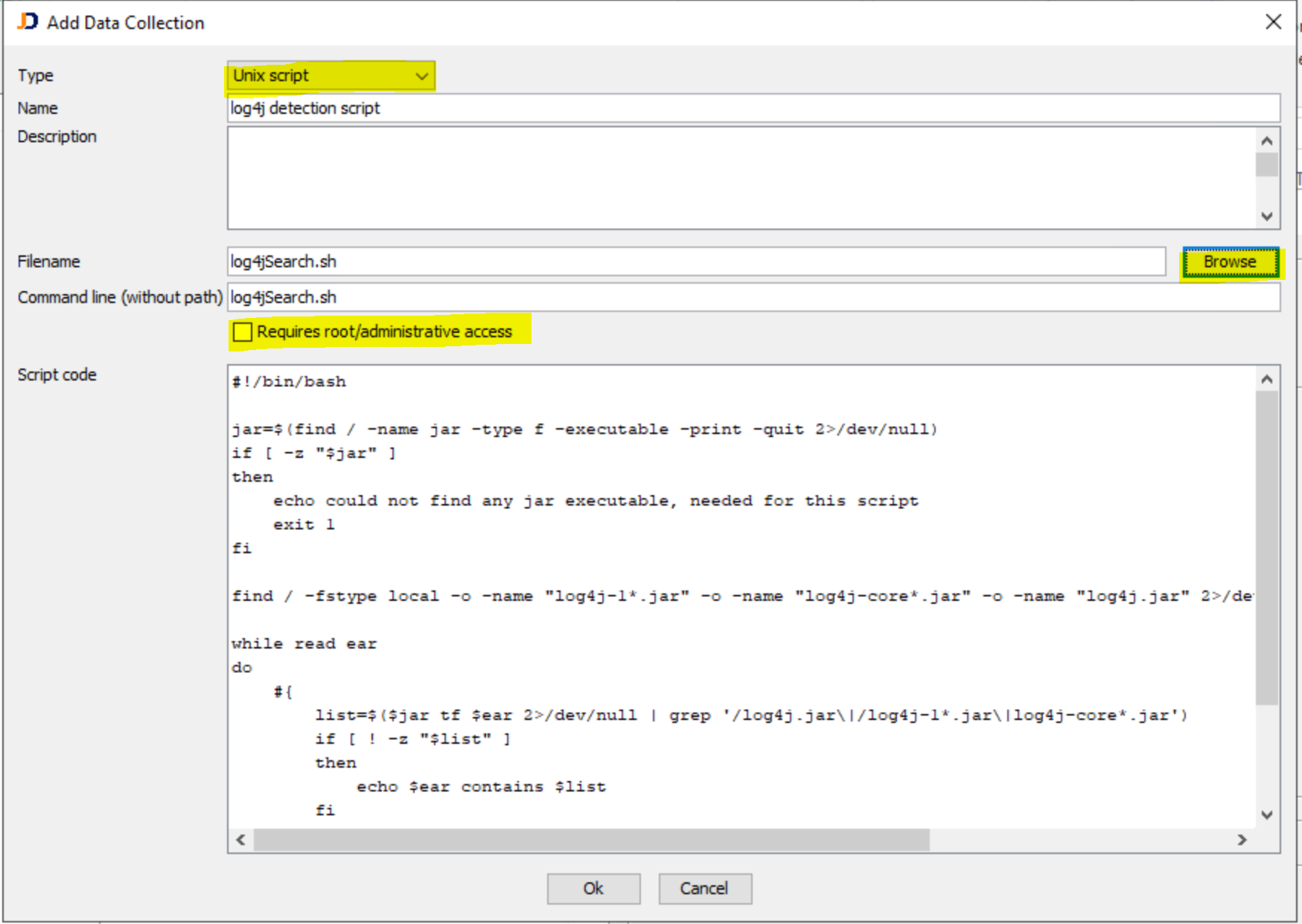
Now, guess what? Click on the Add button to finally add the new script. Make sure to select the type Unix script (or Windows VBS File for Windows). Then use the browse button to locate the downloaded shell script and select it. After selecting the script, the dialog will populate the filename, the command line, and the script code. You might choose the Requires root/administrative access when you have root or administrative access to your Linux computers (this option does not exist for Windows since we are running the scripts as System user). Otherwise, leave it unchecked. In this case, the script gets executed as an ordinary user (the actual scan user), and therefore, it might not have access to all files on the file system.
Close this dialog with Ok and close the next dialog (Custom Attribute Data Collection) also with Ok. Now in the remaining dialog make sure to select your new script. Selecting the script associates the custom attribute data collection for the selected operating system (in this case Linux) with the actual script.
Now, you are all set and you can simply run the discovery for a device. The scan might take a little longer because the script checks the whole file system which might take a while.
Finally, when the discovery is done, you can review the results within a device’s custom attribute section. Below the results for an affected Linux system.
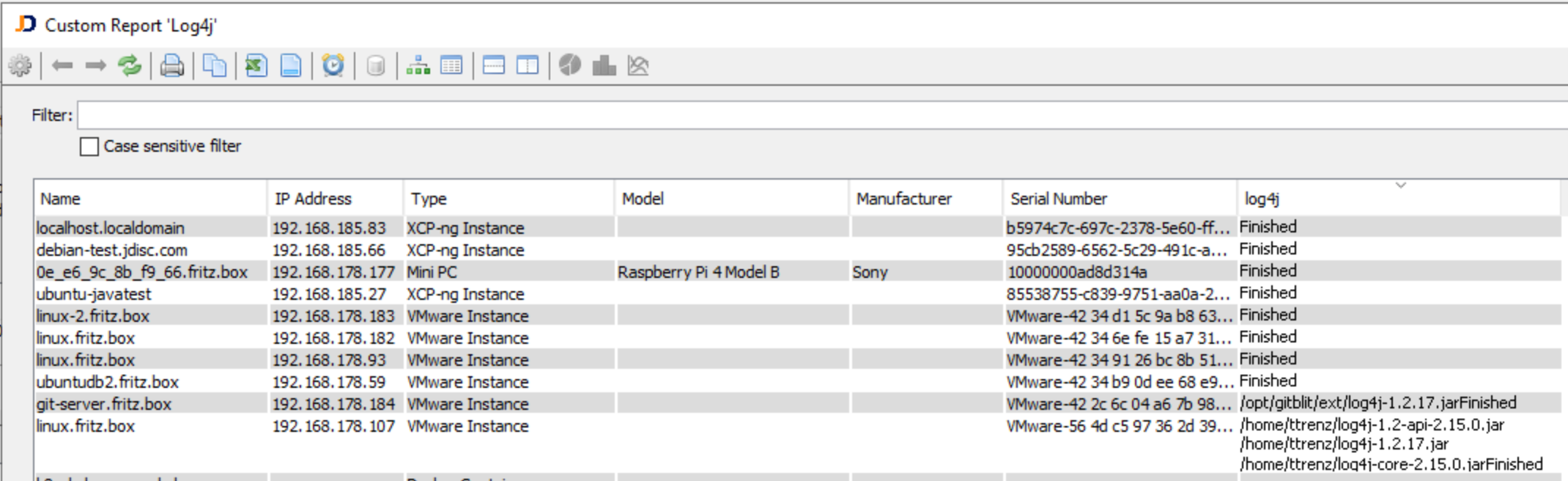
And of course, you can create a custom report having your new custom attribute as a column.