SSH Vulnerability – CVE-2023-48795
Dear JDisc friends,
we have been notified by our SSH client library vendor Jadaptive that there is a critical security issue within the SSH server and client implementations. Refer to the terrapin-attach homepage and check out the CVE-2023-48795 for more details!
What does that mean to you? Well, on the JDisc Discovery side you will be safe with build 5180. We have updated our integrated Putty binary and our SSH client library (https://jadaptive.com/) to their latest releases which fix the issue.
However, you might need to check your SSH servers whether they need up be upgraded. Most Linux servers use OpenSSH. The OpenSSH team has fixed this issue within their latest release 9.6p1.
How can JDisc Discovery help?
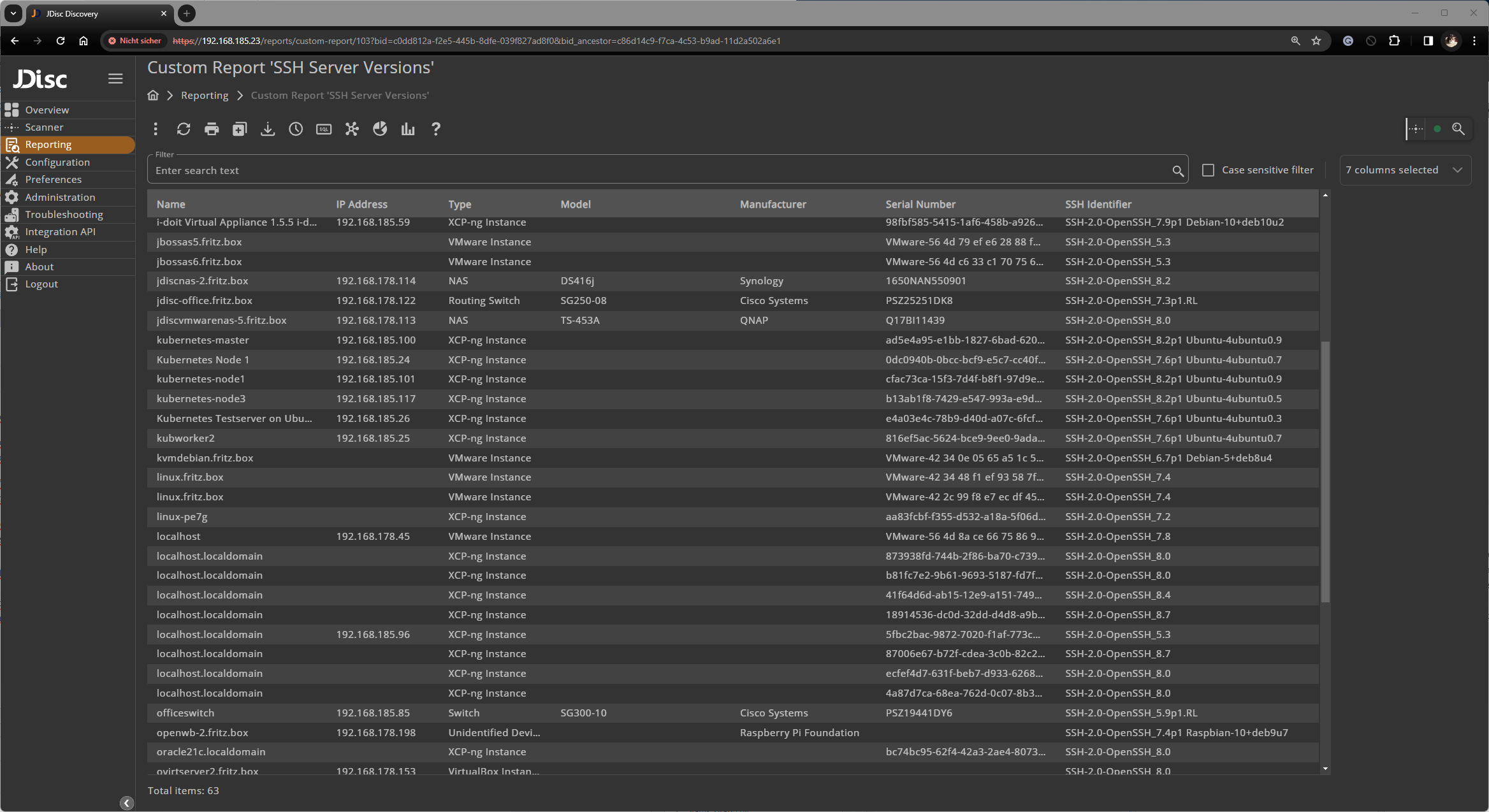
JDisc Discovery is already collecting the SSH identifiers for SSH servers (even without credentials). This feature already exists within JDisc Discovery since 2017. Check out the blog entry describing the feature. SH identifiers usually include the SSH server and version. With that information, you can easily determine what servers to look at and update OpenSSH to the most recent version.
We have created a custom report “SSH Server Versions”. Download the custom report from https://jdisc.com/software/CustomReports/SshIdentifiers.rep and import the report into your installation. As you can see, there is a lot for us to do :-). Note that also other device types like routers and switches might be affected!
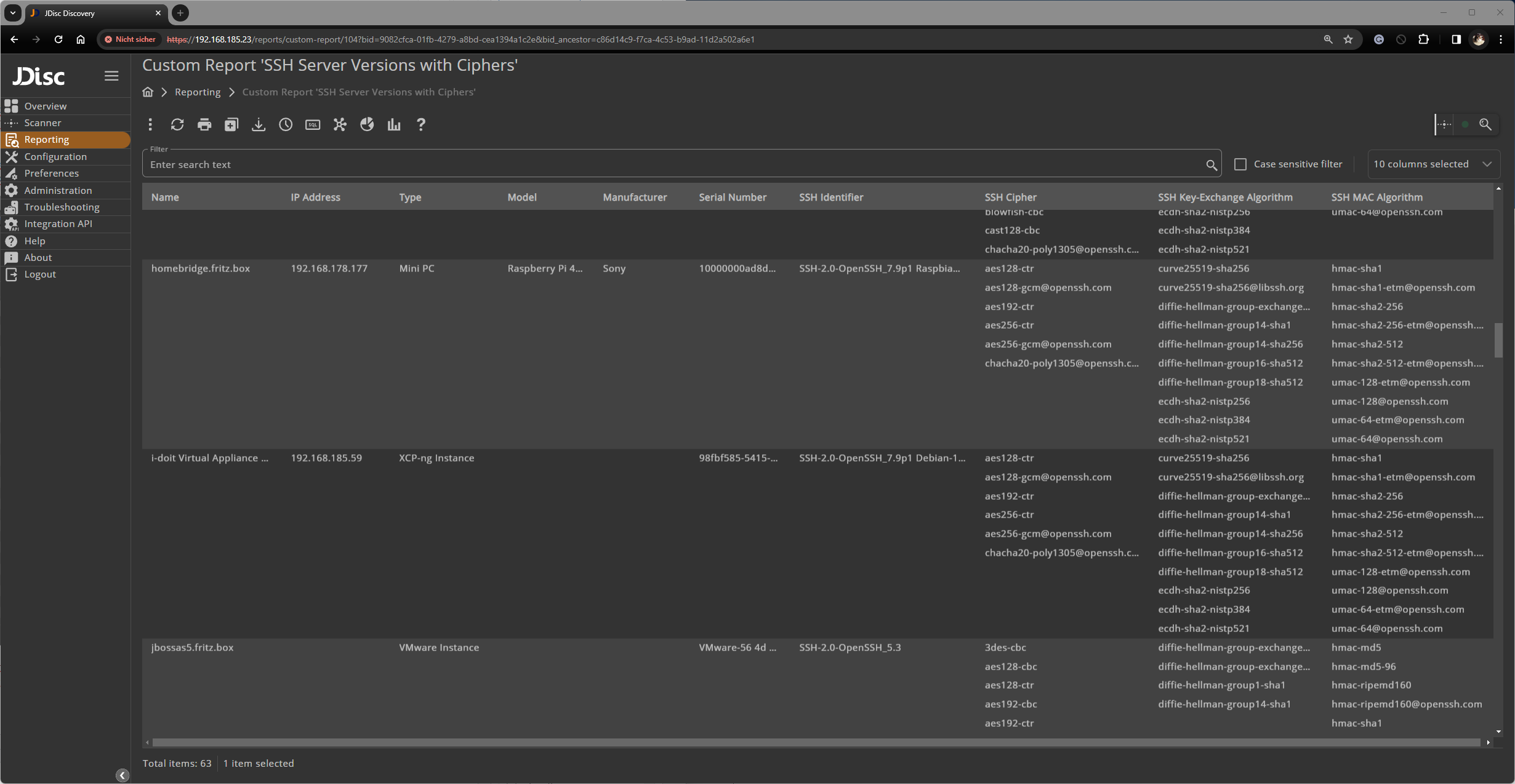
Customers who also licensed the security add on will get more information about the available cipher and key exchange algorithms! Check out our blog entry that describes this feature. The custom report “SSH Server Versions with Ciphers” list all SSH identifiers and the provided ciphers. Download and import the report from here https://jdisc.com/software/CustomReports/SshIdentifiersWithCiphers.rep.
We hope that we can help to make your IT environment more secure!
Cheers,
Thomas
